Dedicated Firewall options for your dedicated server and free Basic Firewall for Virtual Servers and Leaseweb Public Cloud instances.
Dedicated Firewall
For those that they want complete control over the firewall, Leaseweb offers dedicated firewalls that are connected to Leaseweb Private Network.
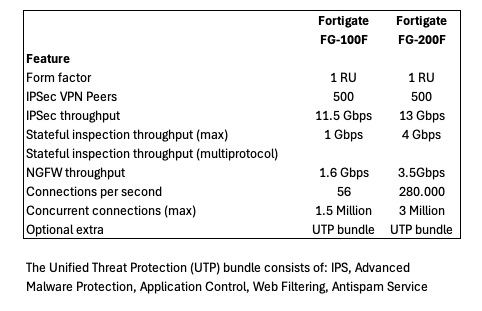
Leaseweb uses Fortinet Fortigate firewalls with the option of having advanced protection capabilities via the UTP bundle.
The Unified Threat Protection (UTP) bundle consists of: IPS, Advanced Malware Protection, Application Control, Web Filtering, Antispam Service)
Leaseweb will do the initial configuration based on your wishes and then you have complete control over the device.
The table below shows the available firewall models and their characteristics:
Basic Firewall for Virtual Servers and Public Cloud instances
Leaseweb offers free Basic Firewall functionality as a feature for Virtual Server and Leaseweb Public Cloud instances to provide basic filtering functionality. This firewall is applied “in front off” your instance on Hypervisor level. By default, the Basic Firewall is switched off. When you switch on the Basic Firewall, all established connections will remain active and functioning until manually terminated. After it is switched on, all incoming IPv4 connections to your cloud instances will be denied, with the exception of specifically allowed connections which you define through rules. You can create these exceptions (rules) before or after switching the basic firewall on.
Information
- IPv6 traffic is not filtered by this firewall.
- The Basic Firewall is stateful. Established TCP connections will not be filtered.
- Leaseweb always recommends employing a second layer of security, such as using iptables or Windows firewall on your Virtual Server and Leaseweb Cloud instances.
The Basic Firewall is not available to VMware-based Virtual Servers (deployed before March 19, 2012) and Premium Virtual Servers. If you want to know if your Virtual Server instance has a Basic Firewall available, check if the option is present in the “Manage” section in the Leaseweb Customer Portal. For certain older deployments, it may be necessary do a single reboot before the Basic Firewall becomes available.